Using OpenTofu/Terraform to create a disposable Tails virtual machine
OpenTofu
Terraform or OpenTofu (the open-source fork supported by the Linux Foundation) is a nice tool to setup the infrastructure on different cloud environments. There is also a provider that supports libvirt.
If you want to get started with OpenTofu there is a free training available from the Linux foundation:
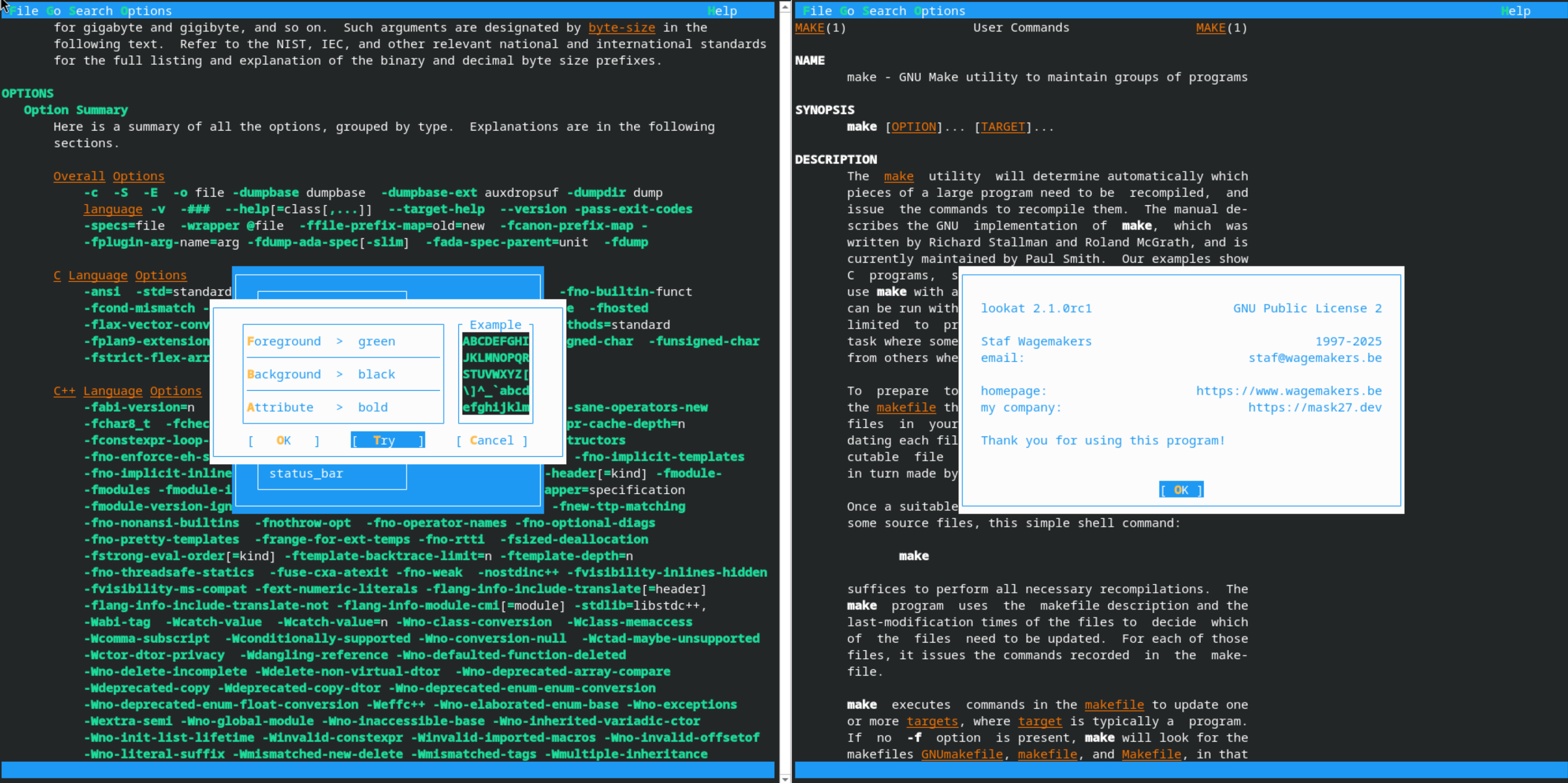
I also joined the talk about OpenTofu and Infrastructure As Code, in general, this year in the Virtualization and Cloud Infrastructure DEV Room at FOSDEM this year:
Read more...